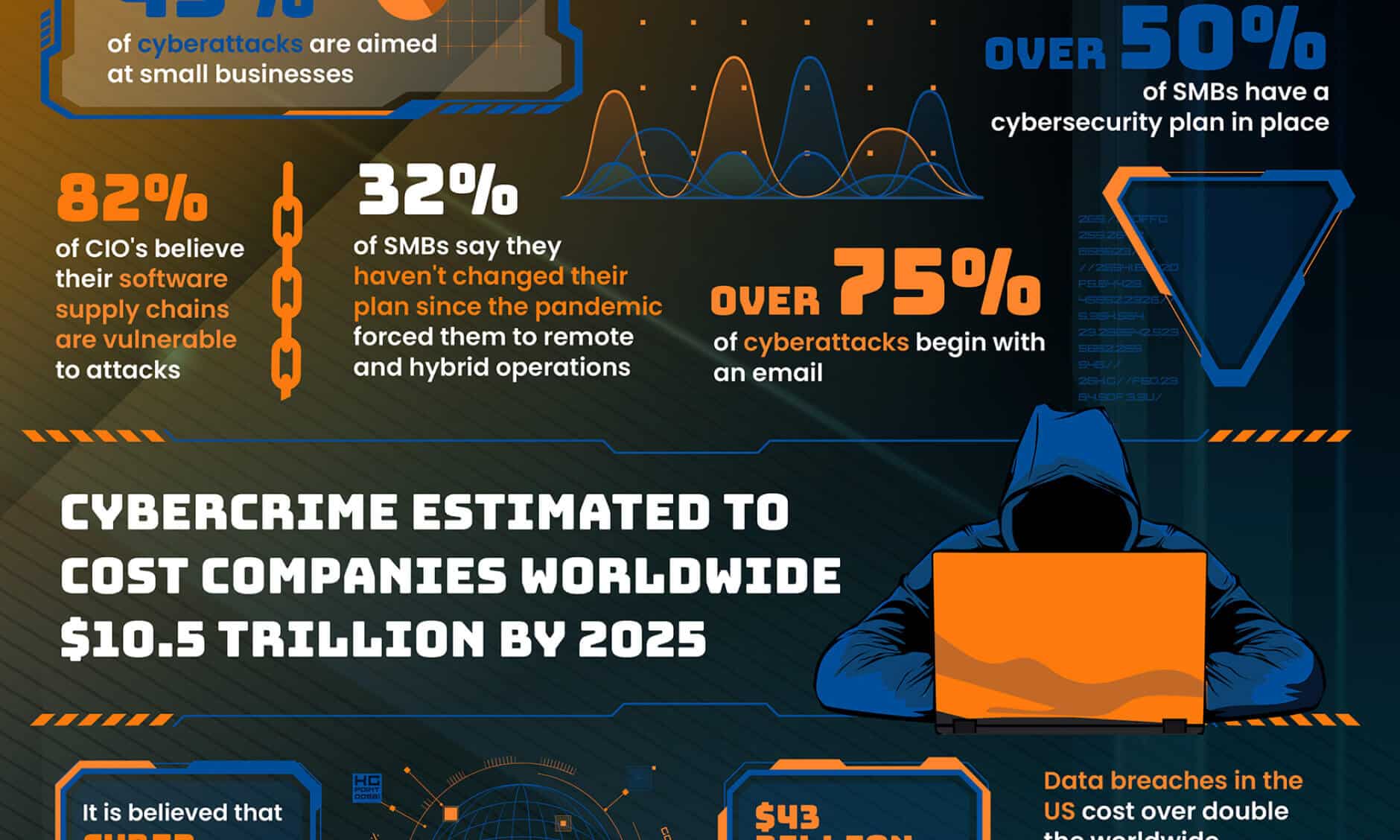
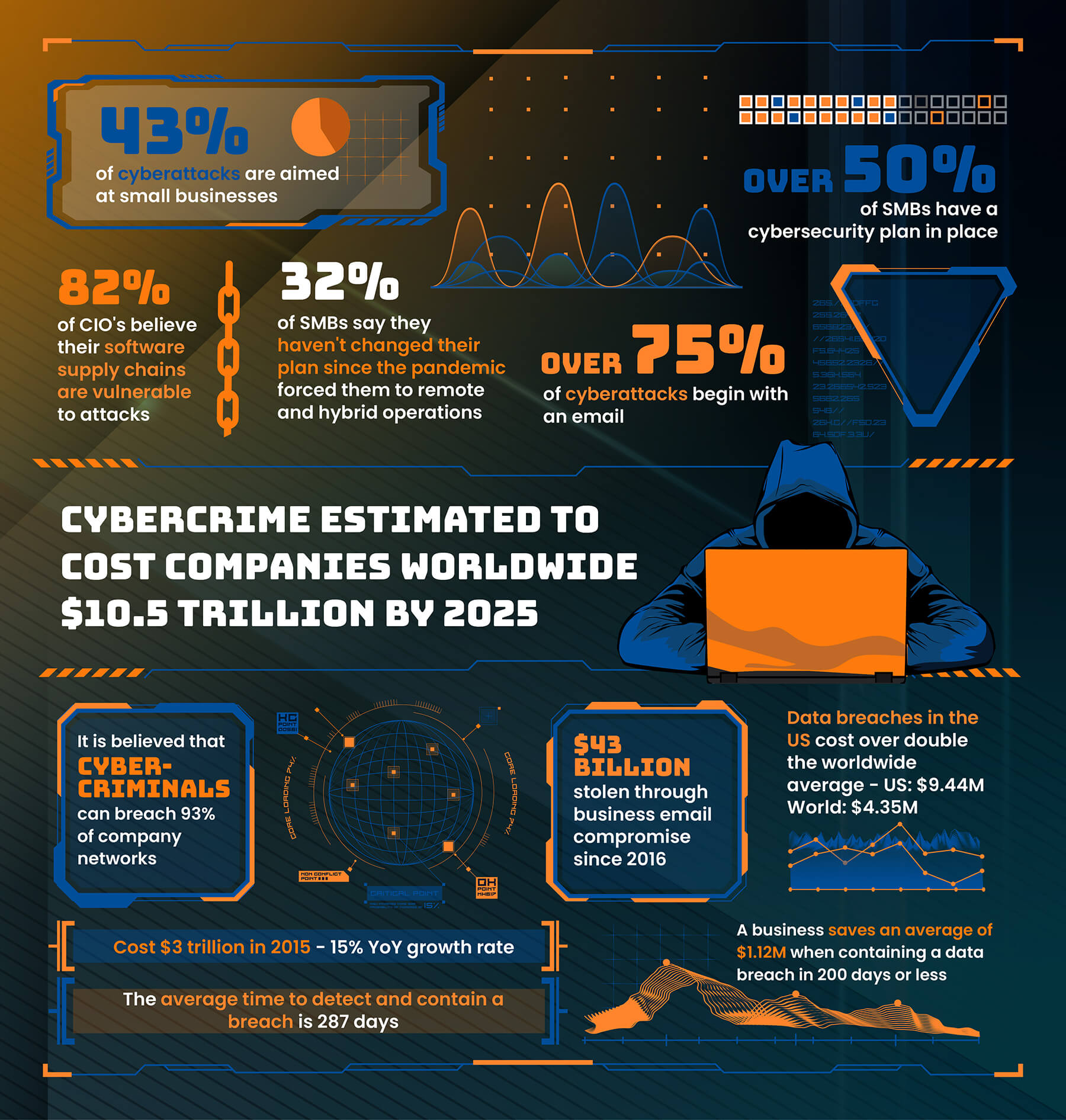
IP addresses sit at the foundation of nearly every digital business decision, yet they are also one of the most misunderstood components of the internet. As VPN usage, privacy relays, and anonymization services continue to grow, organizations are under increasing pressure to understand what an IP address really represents, how trustworthy it is, and what risks or opportunities it introduces by use case.
For security teams, this may mean distinguishing a benign corporate VPN from a risky anonymizer. For media, ecommerce, and compliance teams, it can mean determining whether traffic is coming from a legitimate user, a privacy relay, or a commercial VPN endpoint that could undermine licensing, fraud prevention, or regional enforcement.
To help businesses navigate this complexity, Digital Element created The Definitive Guide to Understanding IP Addresses and VPNs and Implications for Businesses, a comprehensive white paper designed to establish a practical, business-ready understanding of IP address intelligence and IP geolocation.
Why Understanding IP Addresses & VPNs Matters for Business
Most people are familiar with IP addresses and the role they play in connecting devices to networks. Many organizations already rely on IP address intelligence to support day-to-day operations, whether that’s targeted advertising, cybersecurity enforcement, fraud prevention, or compliance with global licensing and regulatory requirements.
What’s far less understood is how different types of IP addresses behave, how VPNs and privacy technologies complicate attribution, and how to interpret IP signals accurately without overblocking or introducing unnecessary risk.
That’s exactly why subject matter experts across Digital Element collaborated to develop an authoritative resource that demystifies the IP address space and explains how businesses can apply IP intelligence responsibly and effectively.
What This White Paper Helps You Understand
The Digital Element white paper starts at the very beginning, in the origins of the internet, and builds toward modern challenges facing enterprises today. Along the way, it explains:
- How IP addresses are created, assigned, and managed globally
- The differences between IP address types and accuracy levels
- How VPNs, proxies, and privacy relays affect IP-based decisioning
- Where IP geolocation data is reliable and where it has limitations
- What signals separate privacy relays from commercial VPN endpoints?
- How can we differentiate legitimate corporate VPN usage from risky anonymizers?
- Can IP intelligence support enforcement without harming user experience?
Chapter Breakdown: What You’ll Learn
Chapter 1: Introduction to IP Addresses
This chapter explores the origins of IP addresses, why they were created, and how they evolved alongside the internet. It defines the many types of IP addresses in use today and clarifies commonly misunderstood concepts such as the differences between static, fixed, and dynamic IPs.
Chapter 2: The Evolution of IP Geolocation Data
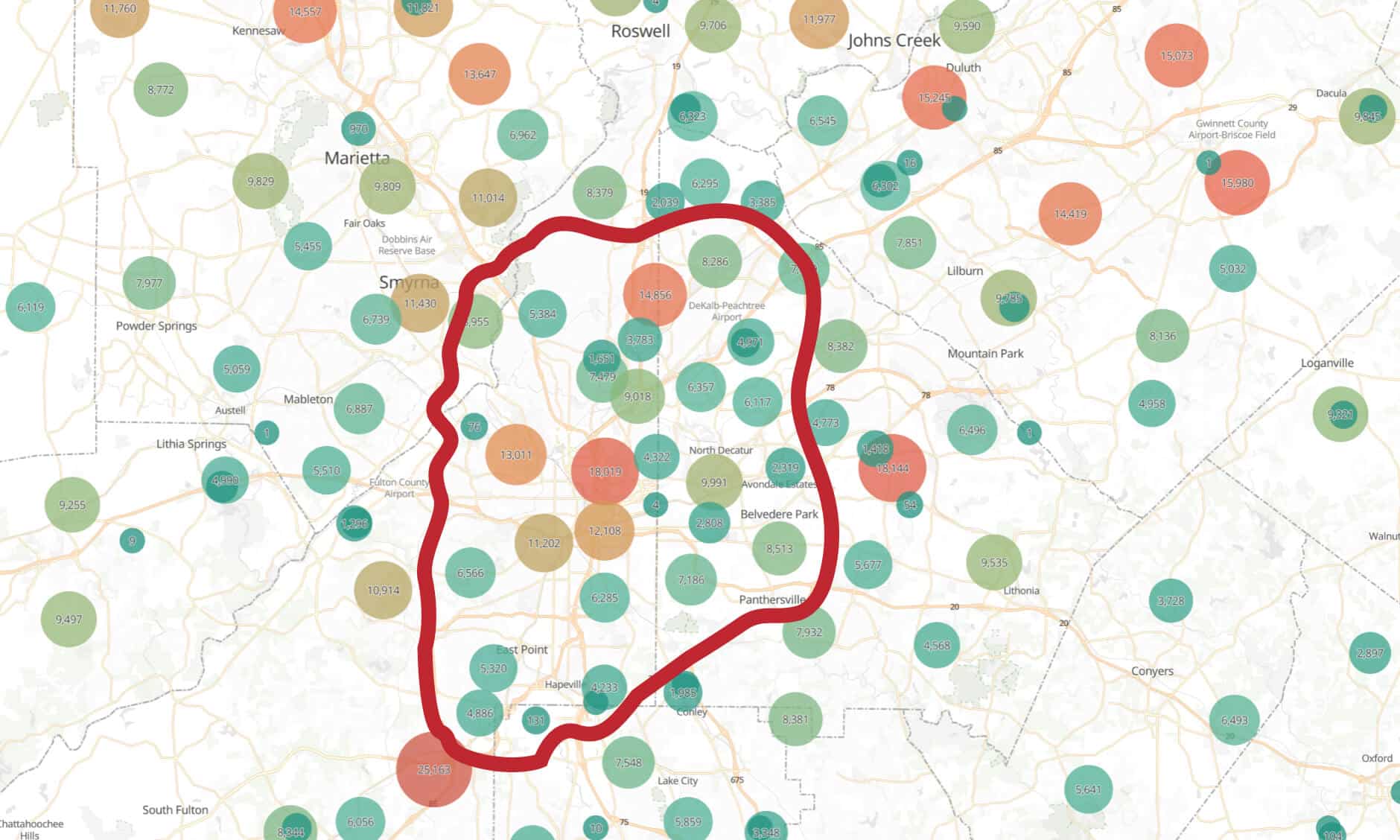
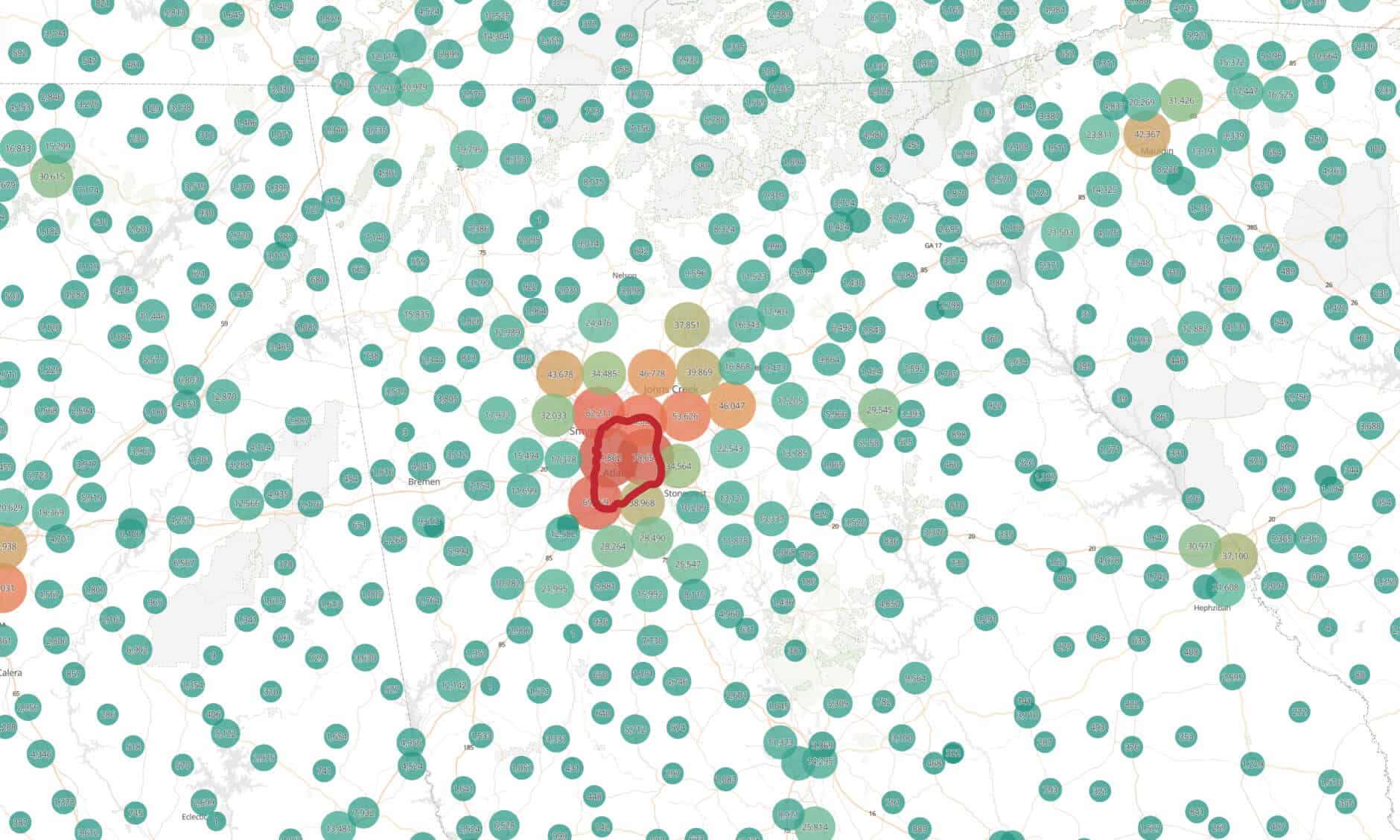
Here, the paper examines how IP geolocation developed and how IP address allocation changed as the internet scaled globally. It explains the impact of IoT growth, IPv4 exhaustion, and the introduction of IPv6, along with critical technologies like NAT and CGNAT that affect address stability and interpretation.
Chapter 3: IP Geolocation Reliability and Vulnerabilities
This chapter looks closely at the strengths and limitations of IP geolocation data. It explores where inaccuracies and vulnerabilities arise, and how Digital Element addresses these challenges through continuous data refinement and contextual intelligence.
Chapter 4: How IP Addresses Are Allocated
Readers gain insight into how IP blocks are assigned to ISPs and enterprises worldwide, why allocation strategies differ, and how these decisions influence IP stability. The chapter also explains how Digital Element leverages allocation knowledge to add meaningful context to IP address intelligence.
Chapter 5: The VPN and Proxy Landscape
As VPN adoption accelerates, this chapter provides a clear breakdown of proxies, VPNs, darknets, and residential IP services. It explains why security and compliance teams need to differentiate between benign corporate VPN traffic and high-risk anonymization services, and how IP intelligence contributes to that assessment.
Chapter 6: Parting Thoughts and Emerging Trends
The final chapter highlights key trends shaping the future of IP geolocation, including 5G adoption, IPv6 expansion, IoT growth, and the continued rise of VPN and privacy technologies.
Why Download the Digital Element IP Geolocation White Paper
Whether you’re responsible for cybersecurity, fraud prevention, advertising performance, or regulatory compliance, understanding IP addresses and VPN behavior is no longer optional.
This white paper equips you with the knowledge needed to:
- Evaluate IP-based risk more accurately
- Understand how VPNs and privacy relays affect IP signals
- Make informed decisions without overblocking legitimate users
- Apply IP geolocation responsibly across business use cases
If you have questions about IP intelligence, VPN detection, or how Digital Element supports enterprise use cases, contact our team, we’re happy to help.