In November, Digital Element announced a new IP address data solution designed to help our customers better understand anonymous traffic, enabling them to make strategic decisions regarding advertising, cybersecurity, DRM, and other use cases.
IPC Characteristics, aka IPC, is the newest addition to our Nodify platform, the industry’s most comprehensive proxy/VPN IP address traffic data. When used together, IPC, Nodify and NetAcuity offer our customers unmatched insights into anonymous traffic, enhancing their ability to understand and manage online activities effectively.
4 Pillars of IPC Metadata
Think of IPC as a vast collection of metadata, meticulously collected, validated and aggregated on a massive scale. This aggregation process unlocks a wealth of valuable insights and information. It has four pillars of metadata, all of which are essential for assessing the relative risk of an IP address.
- Activity. This metric signifies the quantity of devices observed by Digital Element connecting to a particular IP address over a period. This type of data provides insight into the type of location where the wifi is set up, i.e. a public building with many devices or a private space with just a few.
- Geolocation. IPC identifies how many unique locations have been associated with an IP address. As IP addresses are dynamic, the number of geolocations the IP has been seen provides intelligence about the general area it has been seen in, and is an indication of threat level if it has been seen in multiple countries.
- Range. Let’s say an IP address is observed in multiple locations, the next question is what is the distance between those locations. A small average distance may indicate that only one ISP is using it, and it is therefore potentially benign, vs a large average distance which would indicate it could be a proxy.
- Persistence. A unique feature to Digital Element, persistence asks the question: how long has this fixed IP address been at the same location? A greater persistence at a given location indicates the general innocuity of that IP address.
Each pillar serves various purposes and applications. For instance, activity helps advertisers with audience targeting. If you’re an advertiser aiming to target households, and the activity level indicates that over 100 devices are connected to certain IP addresses, it suggests that those IP addresses are less likely to correspond to residential locations.
That sample pillar also helps cyber security teams make smart decisions as to when to prompt users for additional authentication. When the activity level is high, it can serve as an indicator that the traffic originates from a public Wi-Fi service, such as at a local café or airport. This information bolsters threat intelligence and helps cybersecurity professionals assess potential risks and take appropriate security measures.
IPC Metadata and Machine Learning
IPC metadata can be a valuable resource for data scientists looking to enhance machine-learning capabilities and improve their models. For instance, it can provide additional features and context that can be used for feature engineering in machine learning models. These features can help improve the accuracy and relevance of the models.
IPC metadata used to identify anomalies or unusual behavior in network traffic. Data scientists can leverage this data to create anomaly detection models that can help identify security threats or system issues.
Deterministic Data
Another important characteristic of IPC metadata is that it is deterministic, not probabilistic. The GPS coordinates come from the mobile devices themselves, meaning the longitude and latitude information is accurate and reliable. Digital Element also captures the data and time when the geolocation data is observed.
Additionally, the sheer volume of data collected increases the accuracy of understanding traffic, identifying anomalies, and making informed decisions in various contexts, such as cybersecurity and personalized content delivery. This massive volume of data leads to more precise insights and improved performance in IP-related applications.
Why Digital Element is Unique
Digital Element’s ability to collect and analyze billions of IP observations is unique in the IP intelligence data space. This extensive dataset forms the backbone of all our products, and enables our customers to glean valuable insights about the traffic that accesses their networks.
Aggregating this data creates metadata lets us determine context such as:
- Is this IP address coming from a public or private space?
- Can I trust this IP address’s current geolocation? Based on if its dynamic or stable
- Is this potentially a proxy IP address?
- Does this IP address generally always belong to a given geographic region or is it geographically dynamic?
- How much confidence can I have about its given location based on the number of observations at that location?
- How much confidence can I have about its given location based on its last seen location?
Let’s see it in action.
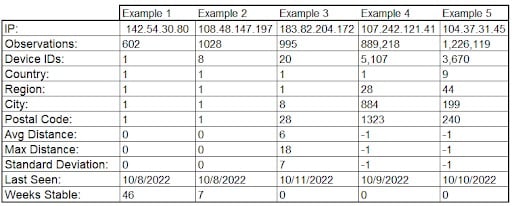
The above table shows five unique IP addresses. From the IP characteristics we can obtain nuanced context of each:
Key Takeaways: Example 1 is a stable IP address based on one geolocation observed over 600 times over 46 weeks. This IP address would likely be considered safe by all measures by a cybersecurity firm.
Key Takeaways: Example 2 is also a stable IP address even though it was only stable for 7 weeks. We see that there were over 8 devices from the same geolocation, making it likely it is a household with multiple computers and mobile devices.
Key Takeaways: Example 3 provides intelligence that this IP address is stable when considering the macro geographic location, but is unstable when looking at the city and postal code level, since it has over 20 devices connecting to it. Even though this IP address is considered unstable, it is likely safe due to the fact that the average and maximum distance between all the postal codes is small. This fact indicates that this IP address is likely a regional NAT. It is likely in a rural area where there are not enough IP addresses allocated there (unstable dynamic one).
Key Takeaways: Example 4 (mobile activity) and Example 5 (proxy activity) are clearly proxy IP addresses given the number of observations and devices connected to them being extremely high. However, the key difference is that Example 4 could be a corporate proxy IP address (relatively less malicious) given that it stays within the same country.
Key Takeaways: Example 5 has been seen in 9 countries. This IP address is clearly one that should be blocked when considering access to secure content.
IP Address Intelligence Experts Since 1999
Since our founding we have sought to provide context to anonymous traffic.
We started in the 1990s helping advertisers accurately and non-invasively target audiences based on their IP address. Since that beginning, we’ve been on a mission to provide as much IP address intelligence and data-driven context as possible to deliver even more value across many verticals.
Our product suite includes:
| NetAcuity | Shines a spotlight on geography, delivering critical insights into location data |
| Nodify VPN Characteristics | Provides unique context into VPNs, proxy networks and dark networks |
| Nodify IP Characteristics | Provides deterministic data about an IP address:
|
To learn more about our new IPC database, visit here.