Have you ever entered a search on Google, looking for the best pizza in your area? You type in something like, “best pizza near me,” to have a list or map of local pizza restaurants returned. Well, this is geolocation in action.
Geolocation, as the word might suggest, is the act of locating the geographical position of a device (computer, mobile phone, etc.) that is connected to the internet. It include details such as the country, region, city, zip code or post code, and the coordinates (latitude and longitude).
There are several different ways a business or website can geolocate a device. For some of these methods, the site seeking the information needs to ask for a user’s permission first, while for other methods, they do not.
What are the Different Methods of Geolocation?
Discovering the geolocation of a device can be achieved in more than one way. The three primary methods of accessing the location of a device are device-based geolocation, IP-based geolocation, and a combination of the two. Each method has its pros and cons which we will delve into further.
What is Device-Based Geolocation?
Device-based geolocation discovers the geographic location of devices such as laptops, mobile phones, and smart watches based on GPS and cellular networks.
It works through triangulation, more specifically GPS-tower-device triangulation. For this reason, device-based geolocation is more accurate in densely populated areas such as cities, where there are more people using devices to assist with the triangulation.
In rural areas, the accuracy of the geolocation can falter due to there being fewer users. However, if your device has a GPS chip and a network signal, geolocation services will be able to access its geolocation relatively accurately.
Because this method of geolocation relies on GPS chips inserted in devices, companies are not allowed to access it without the user’s permission. Websites and apps need to ask to access a user’s geolocation, and location services on the device must be turned on.
For this reason, companies can utilize another form of geolocation that doesn’t require them to ask for a user’s permission first, which brings us to server-based geolocation.
What is IP-Based Geolocation?
IP-based geolocation, also known as IP address geolocation, is a method of geolocation based on the IP addresses of internet-connected devices. IP, or Internet Protocol, addresses are numerical codes assigned to every device that connects to the internet.
IP addresses are typically assigned by internet service providers (ISPs). ISPs tend to use a range of IPs within certain geographical areas, which is how geolocation services are able to provide location data of devices with IPs.
When an internet-connected device attempts to connect to a website, certain information is exchanged between the site and the device. One piece of information that the device shares with the site is its IP address.
That IP address is then sent to an IP-to-geolocation database where it is determined in which geographic area it is used by the ISP, thus revealing the approximate location of the device.
While accessing an IP address can provide certain information about a user, such as the connection type and approximate location, it doesn’t reveal any personal information. Therefore, companies do not need to receive permission from a user to geolocate their device through IP-based geolocation.
IP-to-geolocation databases are operated and maintained by geolocation service providers. Each service has its own means of obtaining and sorting the data, some more accurate than others.
As such, the accuracy of IP-based geolocation depends upon the ability of the geolocation provider processing it. Moreover, ISPs tend to shuffle IPs through various users within an area, adding another layer of complexity to the process.
While device-based geolocation works better in densely populated areas, IP-based geolocation typically works best for larger scale purposes. For example, if a company wanted to geo-target an entire country, or users in a specific postcode, IP-based geolocation would be more suitable than device-based geolocation.
How Precise is IP Address Geolocation?
The exactness of IP address geolocation is based on the ability of the service that the client is utilizing. While some services may be able to locate an IP address to within a certain country, others are capable of locating an IP to within a few miles of the exact location.
With that said, geolocation services are becoming more accurate every day. Digital Element’s NetAcuity offering, for example, can target an IP address within a ZIP+4 area. Furthermore, it is accurate at a rate of 99.99% at the country level, 98%+ at a regional level, and 97%+ at a city level—globally.
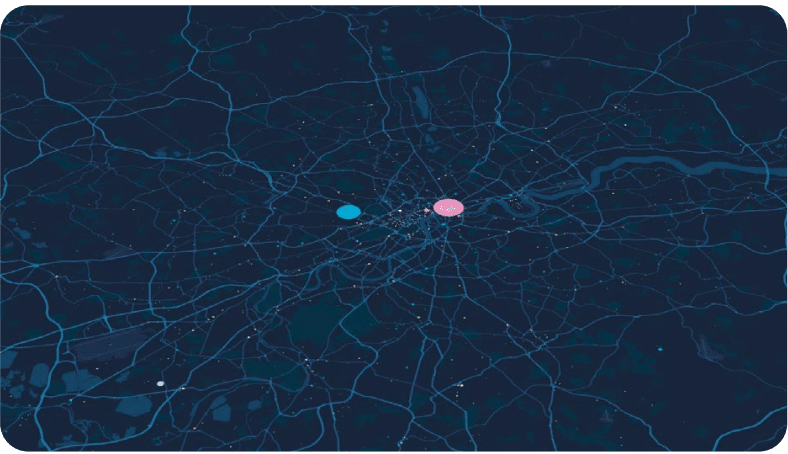
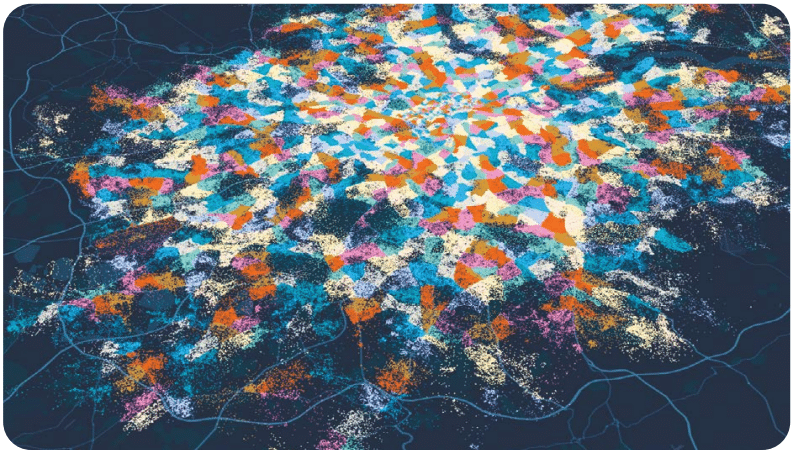
What does IP data granularity look like? The first image below shows the traditional way IP geolocation providers place IP addresses throughout a city—aggregations at certain points on the map, in the case below, the city center of London. The second image shows how Digital Element maps IP addresses to locations appropriate to their populations.
Watch the video below to hear Digital Element’s Chief Product Officer, Vinod Kashyap, details the innovative methodologies Digital Element uses to achieve unrivaled IP geolocation accuracy and coverage.
This level of accuracy and granularity provides for more reliable IP geolocation identification, allowing businesses to focus more specifically on geographically relevant areas. Organizations can leverage this granular, reliable data for enhanced insights, greater campaign performance, and even improving fraud and cyber threat protection.
What is Combined Data Collection?
As both of the aforementioned methods have their pros and, more importantly, their cons, combined data collection utilizes the best of each in an attempt to be as accurate as possible.
If a company’s goal is to target ads within a state, server-based geolocation would be the best option. However, if the same company wanted to target potential customers within a specific brick-and-mortar location, they would be better off turning to device-based geolocation. Combined data collection allows one company to do both relatively well.
Furthermore, one might be preferable to the other based on what a user has or hasn’t allowed. For instance, if a user has not allowed a site or app to track its location through their device, then businesses have no other option than IP-based geolocation, but that doesn’t mean they want to forgo device-based geolocation altogether as other users may be fine with making their location available.
What are the Benefits of IP Geolocation?
At its core, IP geolocation technology enables you to pinpoint users’ geographic location from just their IP addresses, as well as uncover numerous other actionable insights such as:
- Geolocation data (country, city, ZIP/postal code)
- Approximate longitude/latitude
- Proxy data (e.g. masked IP data that can be used by fraudsters)
- VPN intelligence data (provider, features, node type, activity timestamp, etc)
- Connection type / Connection speed
- Mobile, static, dynamic
- Company name that owns that IP address
- Organization name, which is the organization associated with an IP’s corresponding WHOIS range
- And much more…
These insights can be used for applications including online advertising, content localization, digital rights management, legal compliance, analytics, fraud detection and cybersecurity.
Furthermore, IP geolocation data is a powerful asset that solves a wide array of challenges that businesses face today, including:
- The death of cookie-based tracking for marketing and advertising initiatives
- Revenue loss and fines due to violations of licensing and copyright agreements
- Fines and reputational risk from non-compliance with local regulations
- Cyber security threats, including data breaches
Let’s take a look at how IP geolocation technology can be used to address some of today’s online challenges.
Geolocation Data and Marketing
Inherently privacy compliant, IP data is capable of driving strong performance for a variety of marketing initiatives, all while detecting and preventing click fraud and ensuring positive experiences for the user.
Target audiences by longitude/latitude, proxy data (e.g. masked IP data that can be used by fraudsters), home vs. business usage, company name and even carrier data. What’s more, because every device that’s connected to the Internet has an IP address, marketers can target every digital channel, including CTV.
IP geolocation data can also help marketers build more nuanced profiles of their customers by merging it with their first-party data. They can also infuse greater context into every customer interaction, and answer questions such as: where was the device located when it interacted with our brand?
Marketers can enhance analytics by importing IP geolocation data in their martech platform to gain additional insights and make strategic business decisions based on factors such as customer concentration. It can also verify that the correct audience was reached (e.g. right region, business vs. home traffic).
Geolocation Data and Digital Rights Management
IP-based geolocation data helps companies ensure adherence to licensing and copyrights agreements. Programming content (and ads) are served to users based on their precise location (ZIP+4 or POSTCODE).
Moreover, IP address intelligence data includes VPN and Proxy identification. Streaming and broadcast websites that use IP geolocation data are able to identify audiences who have masked their location in order to access content to which they’re not entitled under the licensing agreement, an urgent issue, as 20% of potential video revenue is lost due to piracy.
Beyond compliance, IP intelligence data provides a host of benefits to streaming companies and broadcasters. For instance, because IP intelligence data includes device type and connection type, these companies can deliver content at the optimal speed or format based on the connection type and other datasets.
IP Geolocation Data and Regulatory Compliance
Nearly every country regulates how specific categories of products may be regulated, including tobacco, weapons, cannabis, pharmaceuticals, alcohol, financial services. These regulations dictate how specific products may be marketed, to whom, warnings that must be included, along with how prominently those warnings must appear with an ad.
The challenge for marketers is that those regulations vary from region to region, sometimes quite significantly. Failure to comply with local laws can lead to significant financial and reputational risk.
IP-based targeting solves the challenge of regional complexity. Every device that is connected to the Internet has a unique IP address, which can be used to identify the critical data marketers need to comply with regulations in every region of the world.
Here’s an example of how IP geolocation data can be used in real life: A sports streaming service that broadcasts regional sporting events around the world can use proxy/VPN databases to determine which IP addresses to geo-block from piracy attempts.
The streaming service can also use other IP information parameters to determine when a potential pirate is using a new proxy IP to try and gain access again.
IP Geolocation and Cyber Security
One of the tactics security professionals now use to stop criminal activity is to incorporate a range of IP data, including geolocation data, into existing platforms and technologies. Websites that use IP geolocation data can detect when a user is connected via a proxy, and assess which kind of proxy is used (anonymous, transparent, public, etc.).
Once the type of proxy is detected, companies can flag potential criminal activities, set protocols for handling this type of “non-human” traffic differently, as well as review the post-facto analytics behind these types of connections.
By incorporating proxy/VPN data on the front-end of online security measures, companies can automatically flag an IP address as suspicious and reject or block the incoming IP from connecting to their service, website or network.
Furthermore, IP geolocation allows security teams to balance risk management. For example, IT administrators can implement smart rules where activity is flagged when they see log-ins from unusual or high-fraud locations. Other geolocation examples include:
- Government – An air-service branch of the government can use IP-based VPN data to filter, identify safe VPNs, then develop traffic exemptions for approved vendors in order to automatically grant access to the agency’s networks and websites.
- Financial Services/E-commerce – Any company that conducts business online and accepts digital payment can incorporate proxy/VPN data to implement smart rules to verify consumer IP addresses automatically, and then determine which transactions to review—and which to approve or decline.
- Cyber Security – Managed security service providers (MSSPs) can use proxy/VPN data as a foundational, front-line layer of fraud-prevention security.
They can use these datasets to help prevent unauthorized network and system access attempts. By understanding how online users access and interact with their clients’ networks, MSSPs can be better positioned to more quickly respond to potential cyber threats when unusual activities occur.
Resources to help you learn more about IP geolocation & intelligence
- The Tricky Science Behind IP Geolocation
- How to Choose the Best IP Geolocation Service
- Applications of IP intelligence and IP geolocation data
- Finding the Perfect Fit: How Digital Element’s Decode Balances IP Precision with User Needs
- The Value of High Quality IP Geolocation Data
- Digital Element’s State of the IP Address Report