In today’s rapidly evolving digital landscape, the power of sophisticated data is undeniable, especially when it comes to IP address geolocation intelligence. As a valued customer of our IP geolocation services, you understand the critical role accurate geolocation data plays in tailoring experiences, enhancing security, and driving business strategies. But when was the last time you examined your IP traffic data to see how it might have changed since your initial data evaluation with Digital Element? Chances are it has been a while – and since the last time we have deployed new techniques to harvest IP address data, launched new products, and continued to improve the insights IP address intelligence can offer.
Let’s dive into what you can expect from an updated data evaluation.
Context is EVERYTHING.
As we’ve shared on this blog before, geolocation is just the beginning of the insights that can be gleaned from IP address data. At Digital Element, our technology enables us to provide sophisticated contextual insights related to IP addresses to help our customers interpret their online traffic with a greater degree of understanding. Our data enhances decision-making by providing valuable information to aid in the process of determining the disposition of IP addresses.
Businesses that benefit from understanding these sophisticated insights include:
- Online streaming compliance
- Fraud Detection and Prevention
- CyberSecurity
- Ad-Fraud
- Online Gaming/Gambling compliance
The IP Address Profile Summary report offers tailored insights into your website traffic, empowering you to make more informed decisions on managing your end-user traffic more effectively.
Below are example insights of IP user traffic, drawn from a sample of 1 million IP addresses. These insights cater to a customer focused on regulatory compliance, ensuring users are accessing content from permitted regions for legal, licensing, and fraud prevention purposes
Proxy Categories.
With the exponential growth in proxy use, knowing what % of your traffic and transactions originate from proxies is an important capability.
Why identify if the IP address is associated with a Proxy?
While we may know the location of that IP address, the end-user(s) tied to that proxy IP could be located virtually anywhere in the world, masking their originating IP address.
What percentage of your traffic is associated with a proxy? What about a residential proxy?
Knowing this information is imperative in flagging potential misuse or bad acting by a website visitor.
Is it enough to understand if an IP address is coming from a proxy?
It depends. Not all proxies are bad, so having the ability to discern the level of risk associated with proxy-related traffic enables companies to deploy enhanced decision-making that can both improve security and reduce friction.
Proxy Risk Level
Depending on your use case, having only the knowledge that an IP address is associated with a VPN or Proxy is not necessarily sufficient information to block it as not all VPNs or Proxies are inherently bad. Having access to high-level information that outlines the level of risk associated with IP addresses can be a key data point in determining how to handle them.
In the data set that we analyzed, a massive 64% of the proxies observed were considered to be high-risk. As such, the potential of a bad actor originating from one of these addresses is high. Flagging “high-risk” IP addresses for further analysis or to halt further activity on the site may very well be warranted.
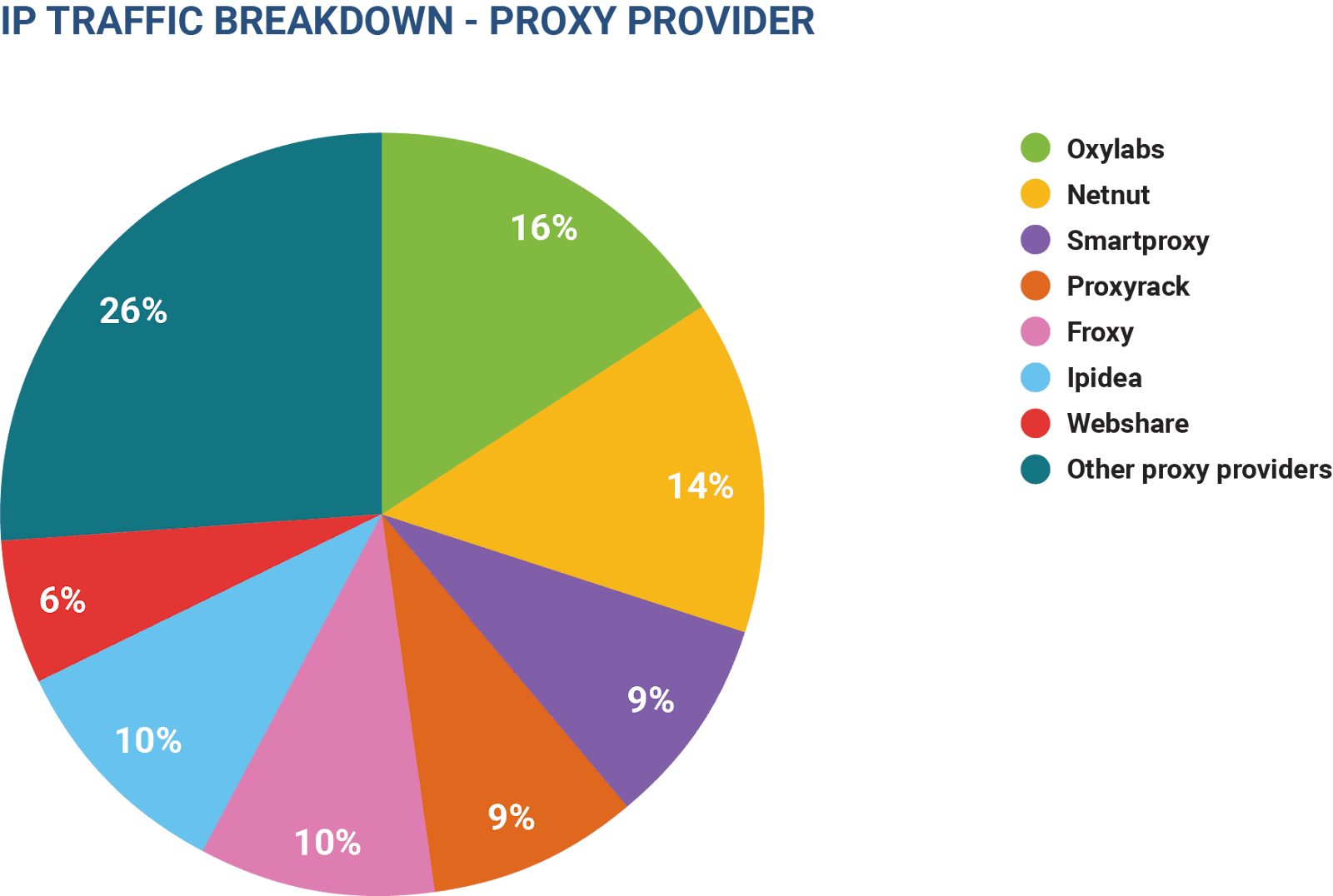
Proxy Providers
As mentioned, not all proxy services are inherently used to mask who they are with the intention of “bad acting”. However, examining the features offered by a proxy provider—such as exit node selection, logging policy details, and the ability to unblock streaming services—suggests that users often seek increased anonymity. This desire for anonymity can arise from a variety of motivations, both nefarious and legitimate. Thus, having more context around a known proxy address provides more intelligence on how to treat that website visitor.
If a higher number of signals associated with malicious activity is seen with the observations of a particular proxy provider, you can then make informed decisions regarding how to manage the traffic tied to these IP addresses.
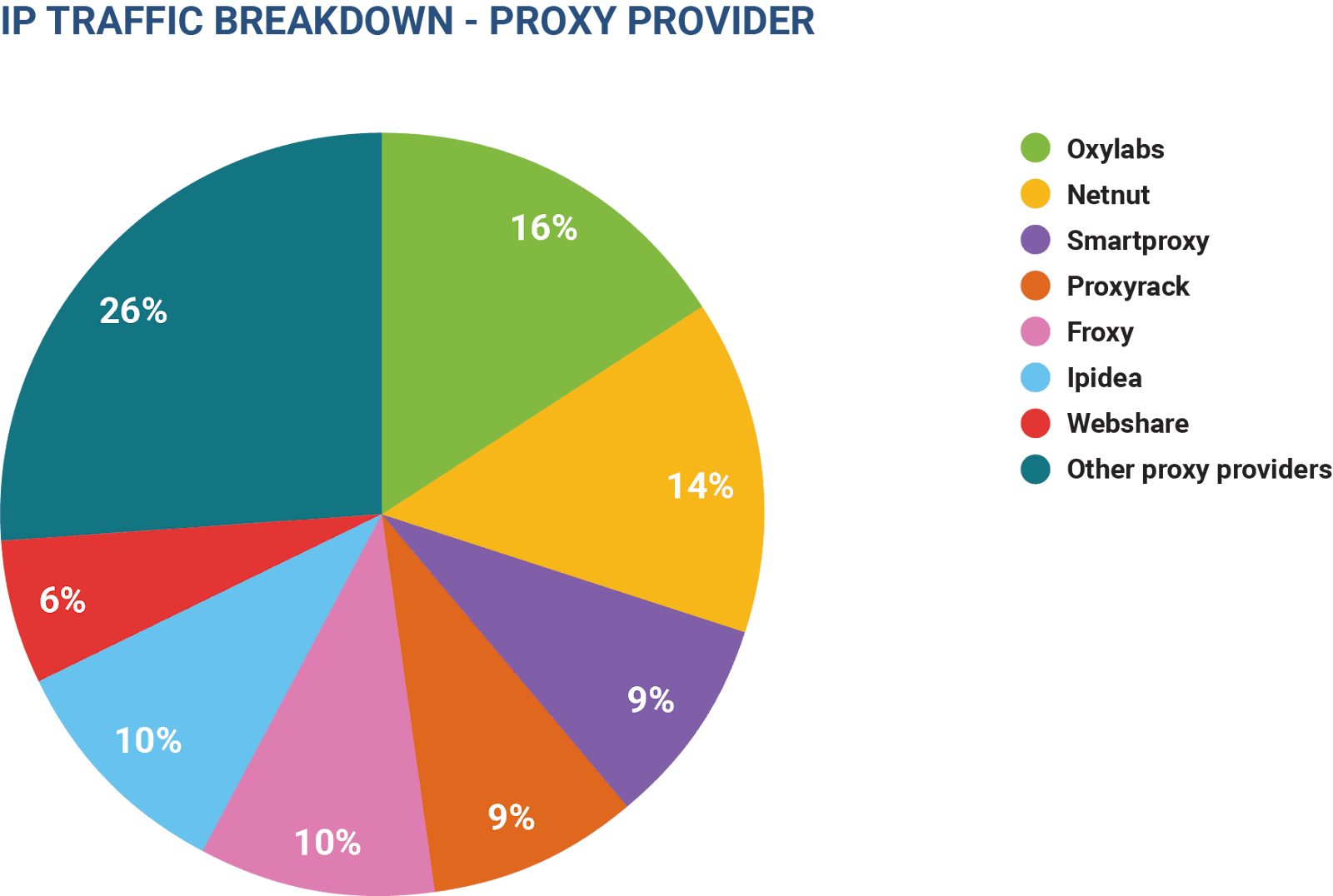
Reviewing past malicious activity or transactions associated with a specific proxy provider can help with decision modeling to identify potential nefarious activity based on those patterns and stop that traffic before it is too late.
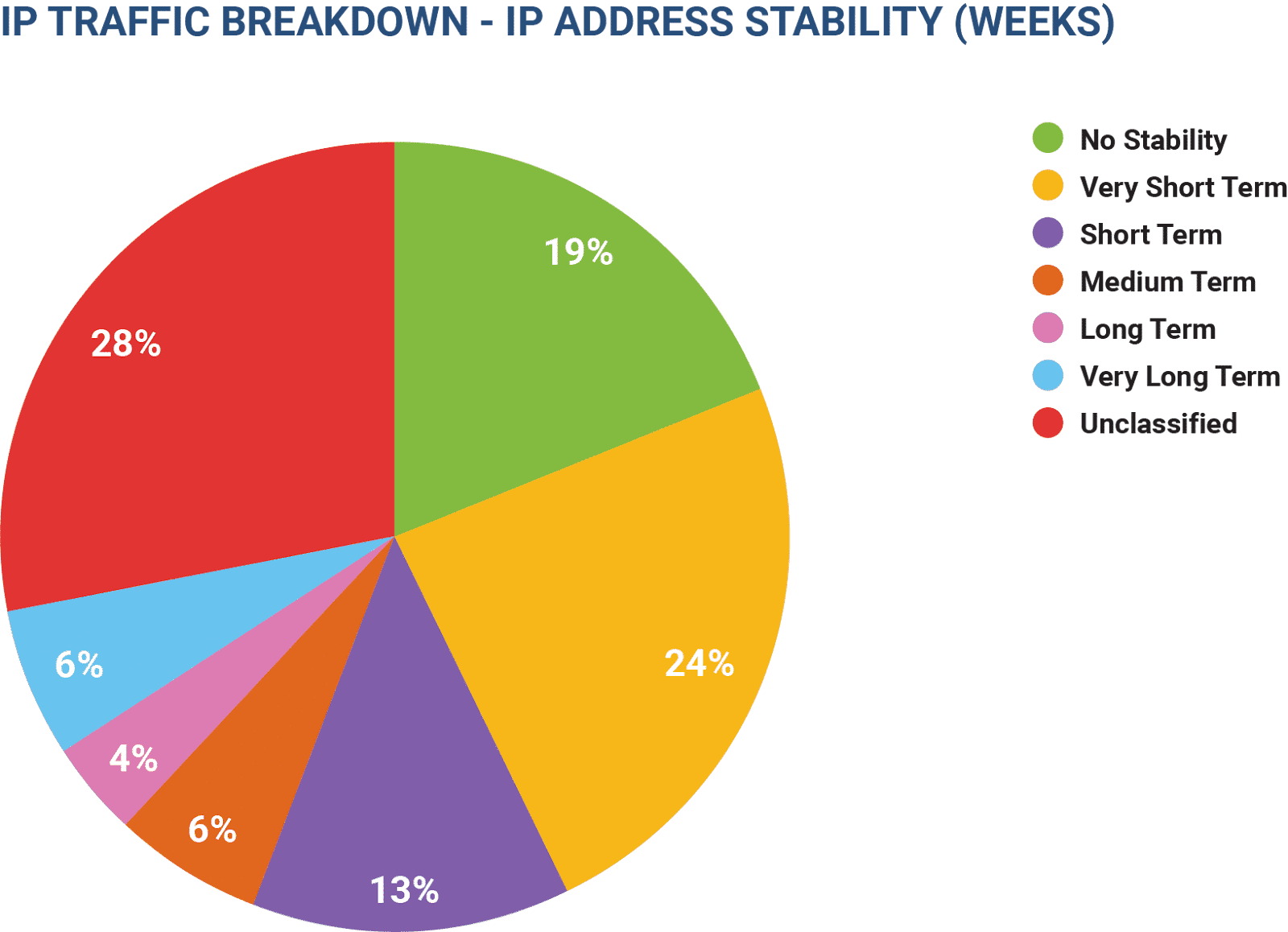
IP Address Stability
Knowing how long an IP address has been stable in a specific location can be a powerful indicating factor in its “trustworthiness.” Generally, an IP address that is less stable should be examined to determine how to treat it. Stability can also be combined with other IP address characteristics like range, activity, or number of devices connected to it to make a decision regarding its disposition.
IP Address Activity Levels
The activity observed in conjunction with an IP address is a great tool to understand how an IP address is being used. If many different devices have been observed this could indicate that the IP address is in a public location, like a coffee shop. If a low count, say less than 10 devices, are observed then it is likely safe to assume the IP address is private.
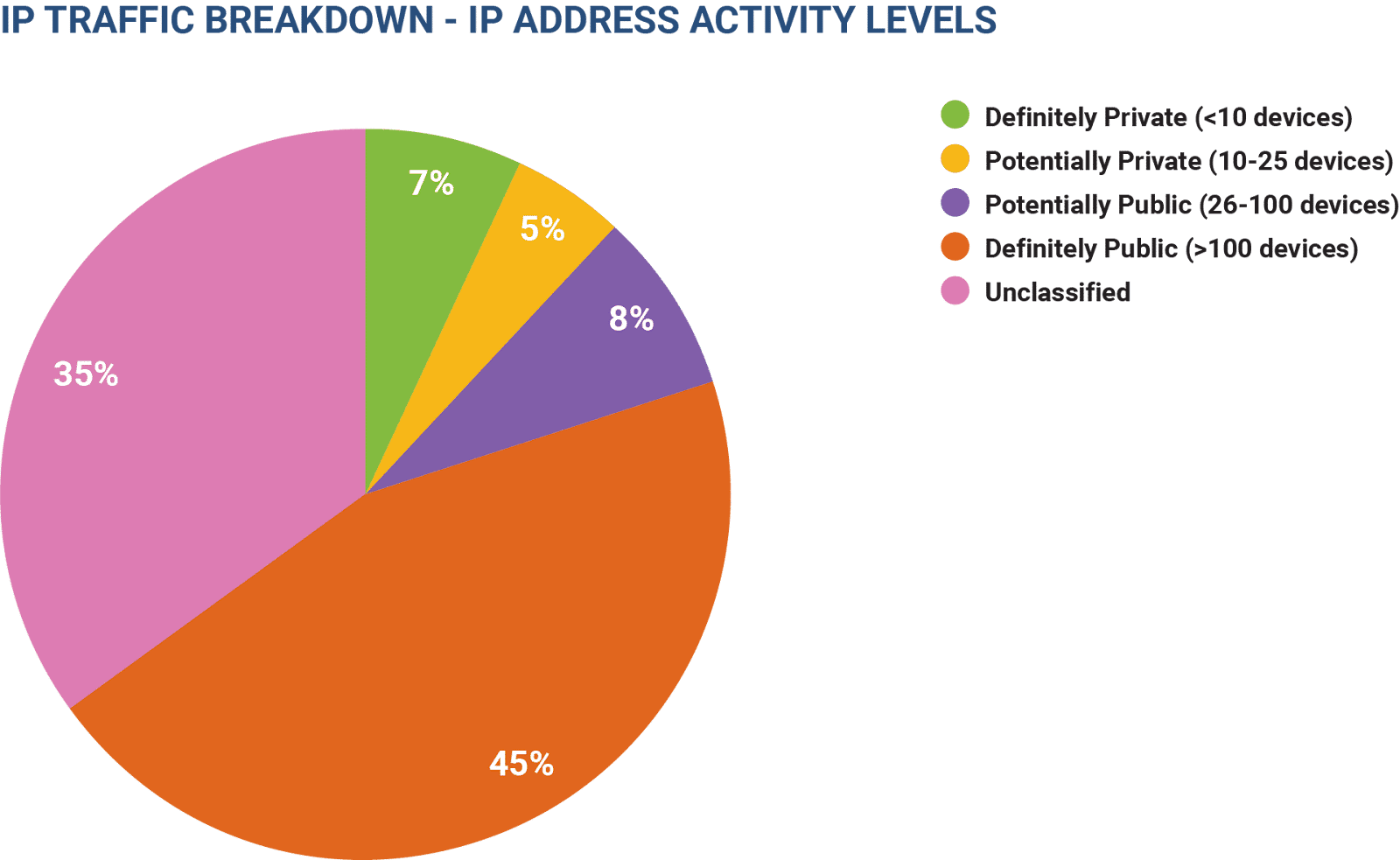
Combining Device ID count with address stability allows you to zero in on which IPs are likely visits from the same end-user week over week.
In sum, understanding the deeper nuances and characteristics around an IP address can significantly enhance understanding of website traffic and associated characteristics, thereby enabling a more nuanced approach to engaging with visitors.
This data allows for the implementation of comprehensive KYC (Know Your Customer) measures, essential for establishing the legitimacy of users and maintaining security standards. By analyzing IP addresses, one can discern patterns of behavior, preferences, and potential red flags indicative of suspicious or fraudulent activity. This information empowers businesses across various sectors to tailor their interactions appropriately, ensuring a personalized and secure user experience while mitigating risks associated with nefarious behavior. In essence, the insights gleaned from IP addresses serve as a cornerstone for effective customer management and safeguarding against malicious intent, ultimately fostering trust and confidence in online interactions.