Streaming providers occasionally encounter situations where legitimate subscribers are blocked because their IP address appears to be operating as a VPN or proxy. In many cases, neither the subscriber nor the ISP has intentionally enabled any anonymization service, which can make these blocks difficult to explain and even harder to resolve.
What’s often misunderstood is why this happens. These classifications are not based on who owns the IP address or how the ISP’s network is designed. Instead, they are driven by observable traffic patterns. When an IP shows behavior that resembles how modern residential proxy networks operate, it may be flagged—even if the IP itself was issued by an ISP and is being used by a legitimate household.
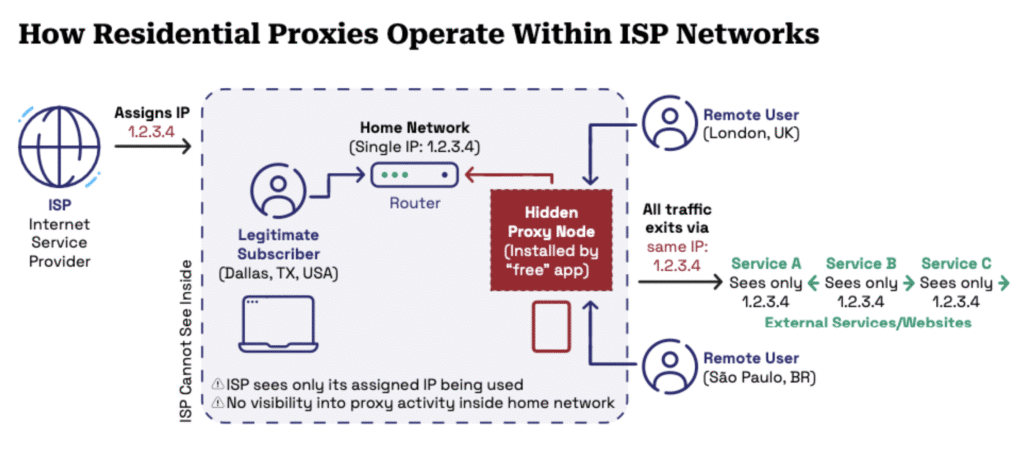
As the internet has evolved, so has the way proxy networks are built. Today, many residential proxies do not rely on traditional data centers. Instead, they quietly operate inside real households using ISP-assigned IP addresses. This shift has made proxy detection more complex for streaming platforms and more confusing for everyone involved.
The Problem: Why Legitimate ISP IPs Get Blocked
A common entry point is the installation of free VPNs, browser extensions, or mobile apps that rely on peer-to-peer networking. These services often include permissions, disclosed only in the fine print, that allow a user’s internet connection to be reused as part of a broader proxy pool.
Once installed, the device becomes a relay node. Traffic from remote users flows through that household’s connection and exits the internet under the same public IP address assigned by the ISP. From the subscriber’s perspective, nothing appears unusual. From the ISP’s perspective, the network is functioning normally.
From the streaming provider’s perspective, however, the IP now carries mixed traffic patterns originating from multiple locations. This behavior closely resembles a residential proxy service, even though neither the subscriber nor the ISP has knowingly participated in one.
Why These Blocks Occur and Why ISPs Are Often Surprised
Streaming platforms make access decisions based on observed risk signals, not assumptions about intent. When an IP shows signs of relaying traffic, geographic instability, or anonymization behavior, it may be blocked to protect licensed content and reduce abuse.
In shared residential environments, such as apartment buildings or managed broadband networks, a single device acting as a relay can impact everyone behind the same public IP. This is why legitimate viewers may be blocked even when they are not using a VPN themselves.
Importantly, this behavior does not originate from ISP infrastructure. Shared IPs and NAT (Network Address Translation) are standard across residential networks and do not cause proxy classification on their own. The activity triggering these signals occurs inside the subscriber environment, outside the ISP’s visibility or control. This is why ISPs are often blindsided by these situations and why ownership of the IP alone does not explain the behavior being observed.
Adding Time-Based Context to Proxy Detection
One of the core challenges in proxy detection is understanding recency. Many systems rely on simple indicators that show whether an IP was seen acting like a proxy within a fixed window of time. These signals lack the context needed to determine whether the behavior is ongoing or historical.
Nodify addresses this by adding time-aware proxy intelligence. Each observed proxy event is recorded with precise timestamps and frequency data. This allows streaming providers to see when proxy behavior occurred, how often it was observed, and whether it is still active.
With this level of detail, platforms can distinguish between a short-lived relay event and sustained proxy activity. This helps reduce false positives while still enforcing content protection policies effectively.
Using Behavioral Signals to Reduce False Positives
While Nodify answers when proxy behavior occurred, IP Characteristics helps explain how an IP is being used over time.
IPC analyzes behavioral and environmental signals such as device counts, geographic stability, and connection volatility. These signals provide insight into whether an IP behaves like a normal residential connection or shows patterns consistent with proxy or automated traffic.
For streaming providers, this additional context helps validate enforcement decisions. IPC allows teams to understand whether unusual behavior reflects normal residential usage patterns or something more anomalous, enabling more proportional responses that protect content without unnecessarily disrupting legitimate viewers.
A More Accurate Way Forward for Streaming Platforms
An ISP-issued IP address no longer represents a single household’s activity in all cases. In today’s internet, many residential IPs are quietly reused as part of proxy networks without the knowledge of the subscriber or the ISP.
For streaming providers, recognizing this reality is key to reducing confusion and improving resolution times. Combining time-based proxy intelligence with behavioral context allows platforms to separate real risk from unintended side effects, protecting content while minimizing disruption for legitimate subscribers.
Frequently Asked Questions
Why would a legitimate ISP IP address be mistaken for a proxy?
Proxy detection systems evaluate observable traffic behavior, not IP ownership or intent. If an ISP-issued IP shows patterns such as traffic relaying, geographic instability, or mixed usage consistent with modern residential proxy networks, it may be classified as proxy-like—even when the subscriber and ISP have not knowingly enabled any anonymization service.
Are shared IPs or NAT the reason these blocks happen?
No. Shared IPs and Network Address Translation (NAT) are standard features of residential ISP networks and do not cause proxy classification on their own. Proxy-related flags are triggered by activity that occurs inside the subscriber environment, not by normal ISP infrastructure or IP sharing practices.
How can a residential IP start behaving like a proxy without the user realizing it?
Some free VPNs, browser extensions, or mobile apps use peer-to-peer networking models. When installed, these tools may allow a device to act as a relay for third-party traffic. From the user’s perspective, nothing appears unusual, but externally the IP may exhibit traffic patterns that resemble a residential proxy service.
How can streaming platforms reduce false positives without weakening enforcement?
By adding time-based proxy intelligence and behavioral context, platforms can distinguish between short-lived, historical proxy activity and sustained risk. This allows teams to make more proportional enforcement decisions—protecting licensed content while minimizing unnecessary disruption for legitimate subscribers.